News
Latest Articles
Our in-house CISO’s views and advices
Your weekly 3 min must-read
- All Post
- Access Control
- AI
- Blog
- E-crime
- Hot
- Phishing

Threat landscape continues to evolve As we reflect on recent cybersecurity incidents, particularly the ransomware attacks affecting organizations like…

A Global Prestige and Most Vulnerable Point In the realm of digital evolution, Sweden digitization has emerged as a…

Artificial intelligence (AI) has become an integral part of our daily lives, from virtual assistants like Siri and Alexa…

Exploring the motives behind the ransomware attack on the Church of Sweden. Uncover the reasons and implications of this…
How did we get to this? Unrealistic expectations of the HR team, insufficiently motivated people, better benefits in other…

Subcontractors as a 2.5 party cybersecurity risk and how to manage them Content of This Tutorial 1. What is…

Introduction Remote work and outsourcing is no longer just a trend, but a reality. Yet you can control remote…

Cybersecurity is no longer just about finding and fixing vulnerabilities in your systems and networks. It isalso about anticipating…
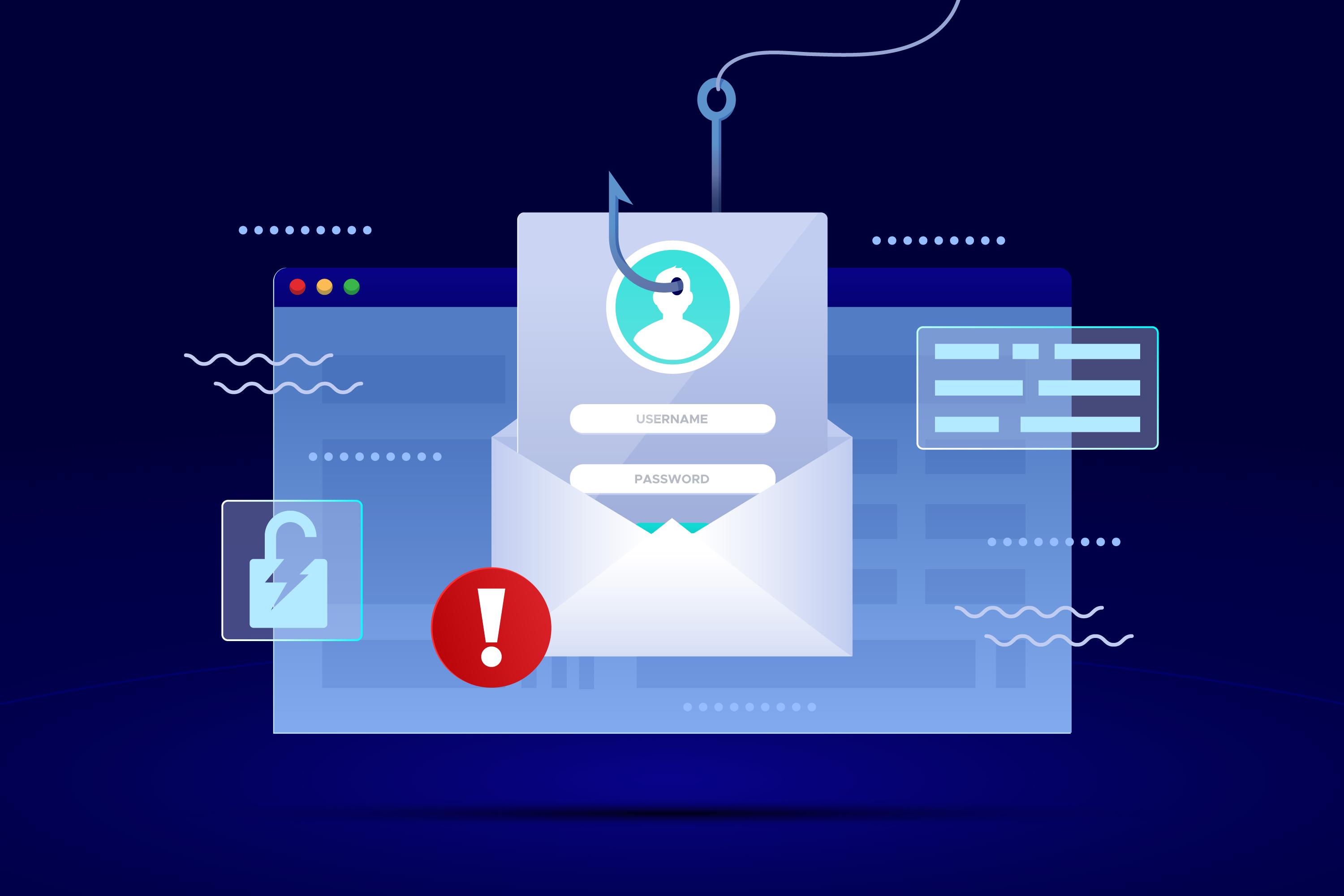
Introduction: In today’s digital landscape, organizations face an ever-growing number of cyber threats, with phishing attacks being one of…

